Triggers
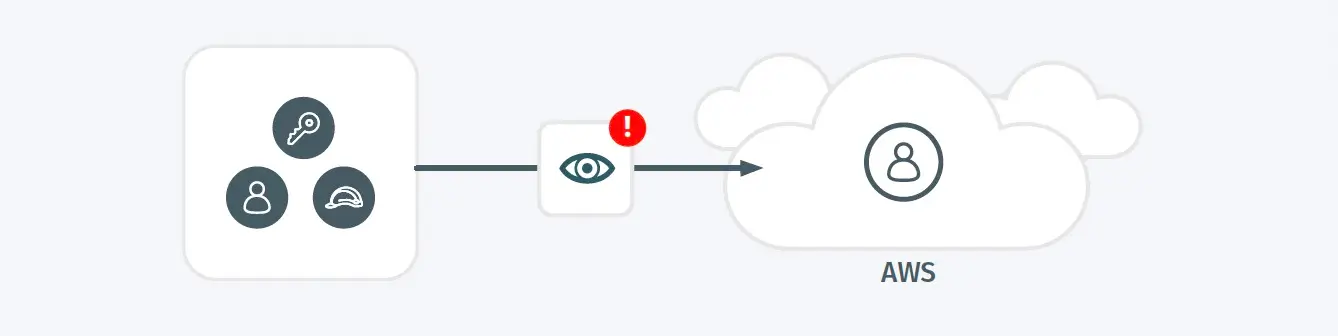
- Credential was observed performing a set of unusual API requests that can be associated with the discovery or subsequent phase of an attack.
Possible Root Causes
- An attacker may be actively looking for privilege escalation opportunities
- A security or IT service may intentionally be enumerating these APIs for monitoring reasons.
Business Impact
- Privilege escalation may indicate the presence of an adversary that is modifying permissions to progress towards an objective.
Steps to Verify
- Investigate the account context that performed the action for other signs of malicious activity.
- Validate that any modifications are authorized, given the purpose and policies governing this resource.
- If review indicates possible malicious actions or high-risk configuration, revert configuration and disable credentials associated with this alert then perform a comprehensive investigation.