Triggers
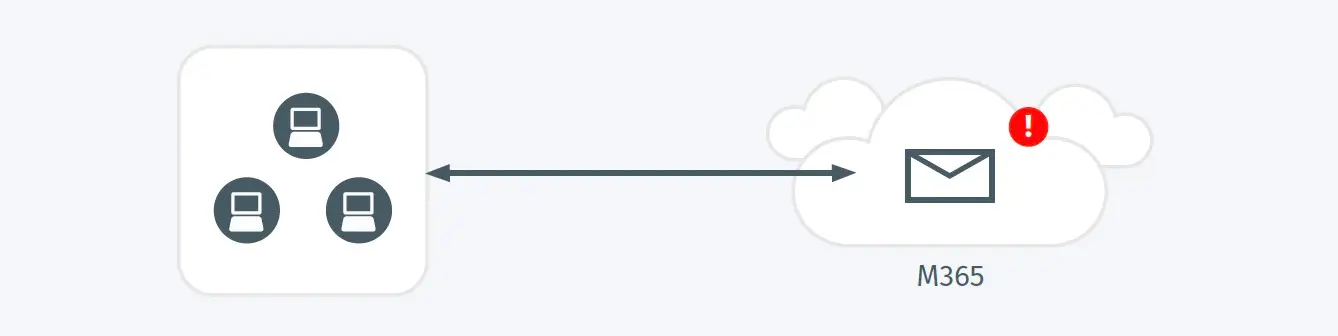
- A user was observed sending multiple emails to internal recipients which were flagged by O365 reputation scanning as likely phishing emails.
Possible Root Causes
- An attacker has compromised a single account and is abusing its access and implicit trust within an organization to attack additional accounts via spearphishing emails.
- Benign emails have been flagged as suspicious based on their content or attachments, which are most frequently associated with invoices sent to distribution lists.
Business Impact
- Spearphishing is one of the predominant ways attackers gain and expand access to credentials within an environment and is particularly effective when utilizing the implicit trust of an internal sender.
- Successful internal spearphishing campaigns result in broad access to a large range of resources within the environment, resulting in a significant increase in overall impact of a compromised account incident within an organization.
Steps to Verify
- Review the details and contents of the email to validate it is malicious.
- Review additional detections and events by the source user which may indicate their account has been compromised.
- Validate the source user is aware of and sent the email that was flagged.