Privilege Anomaly: Unusual Host
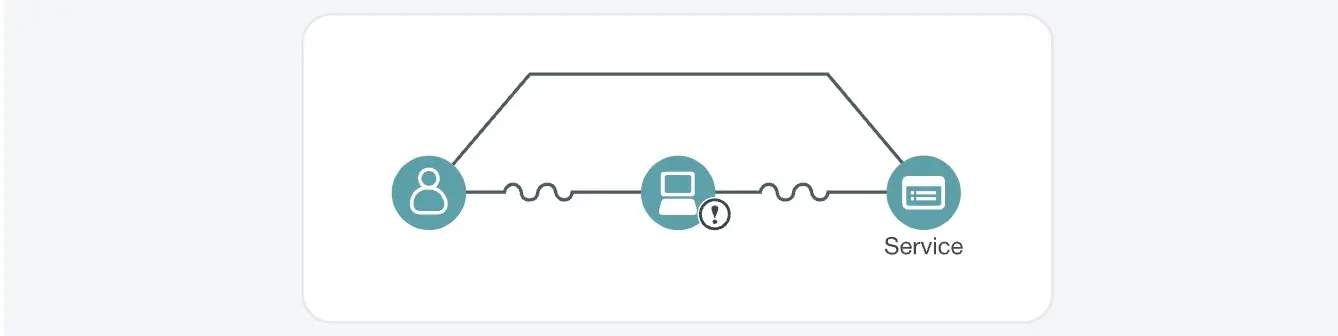
Detection overview
Triggers
- An account is used to access a service from a host which the account is not usually on and from which the service is not usually accessed and at least the service (and likely the account) has a high privilege score OR the privilege score of the host is suspiciously low in comparison to the privilege levels of the account and service
Possible Root Causes
- The account is under the control of an attacker and is being used from an unusual host to connect to one or more services which are normal for the account but abnormal from the host
- An employee or contractor with approved access to the network who pretty consistently works from a particular set of hosts has been assigned a new host or has temporarily decided to work from another host
Business Impact
- Lateral movement within a network involving privileged accounts, hosts or services exposes an organization to substantial risk of data acquisition and exfiltration
- Unexplained unusual patterns of use of privileged accounts, hosts and services are involved in almost all major breaches
- Attacks carried out by rogue insiders will often exhibit unusual patterns of use as well
- The accounts and hosts used and the services accessed provide a possible perspective on the potential business impact
Steps to Verify
- Examine the Kerberos or Active Directory server logs for a more detailed view of activity by this account across all hosts
- Carefully inquire into whether the owner of the host in question should be using the specified accounts to access the listed services
- Verify that the host from which authentication is attempted is not a shared resource as this could mean that the attacker is using it as a pivot point
Privilege Anomaly: Unusual Host
Possible root causes
Malicious Detection
Benign Detection
Privilege Anomaly: Unusual Host
Example scenarios
Privilege Anomaly: Unusual Host
Business impact
If this detection indicates a genuine threat, the organization faces significant risks:
Privilege Anomaly: Unusual Host
Steps to investigate
Privilege Anomaly: Unusual Host
MITRE ATT&CK techniques covered
Privilege Anomaly: Unusual Host
Related detections
No items found.