Identity threat detection and response (ITDR): the complete guide
Key insights
- Identity is now the dominant attack vector. Ninety percent of incident response engagements in 2025 involved identity weaknesses, making ITDR essential for any modern security program.
- ITDR complements — but does not replace — IAM, PAM, EDR, and XDR. It adds identity-specific behavioral detection that other tools lack.
- Non-human identities are an emerging blind spot. With 18.1 million exposed API keys and 6.2 million AI tool credentials recaptured in 2025, machine identity threats demand the same scrutiny as human ones.
- Effective ITDR requires phased implementation and measurable KPIs — including mean time to identify, false positive rate, and identity attack surface coverage.
- Real-world breaches prove the case. The Snowflake, Midnight Blizzard, and FICOBA incidents each demonstrate how identity-based attacks succeed where traditional controls fail.
Identity has become the primary attack surface. In 2025, 90% of incident response investigations involved identity weaknesses, and 65% of initial access was identity-driven — through phishing, stolen credentials, or brute force — according to Unit 42's Global Incident Response Report 2026. Meanwhile, nearly two billion credentials were indexed from malware combo lists in that same year. Traditional perimeter and endpoint controls were never designed to catch attackers who walk through the front door with valid credentials. Identity threat detection and response (ITDR) exists to close that gap.
This guide explains what ITDR is, how it works, the attacks it detects, how it compares to other security tools, and how to implement it effectively — with real-world breach case studies and compliance mapping to back every claim.
What is identity threat detection and response (ITDR)?
Identity threat detection and response (ITDR) is a security discipline that detects, analyzes, and responds to threats targeting user and machine identities across on-premises and cloud environments, using behavioral analytics and AI to identify credential misuse, privilege escalation, and identity-based lateral movement that bypass traditional perimeter defenses.
Gartner first recognized ITDR as a top security and risk management trend in 2022, calling it out as a distinct category separate from identity and access management (IAM). The distinction matters. IAM manages who gets access. ITDR detects when that access is subverted, abused, or stolen.
The market has responded. The ITDR market is growing at approximately 22.6–22.9% CAGR, according to both Fortune Business Insights and MarketsandMarkets. That growth reflects a reality defenders already know — attackers have shifted from exploiting infrastructure to exploiting identities.
ITDR works alongside identity security posture management (ISPM), its preventive counterpart. Where ISPM focuses on hardening identity configurations, right-sizing permissions, and removing dormant accounts before attackers exploit them, ITDR monitors for active threats in real time. Together, they form a comprehensive identity security strategy built on both prevention and detection. Identity analytics provides the behavioral intelligence that powers both disciplines.
Why identity is the new perimeter
The scale of identity exposure is staggering. According to the IDS Alliance's 2024 Trends in Securing Digital Identities study, 90% of organizations experienced an identity breach in the past year. The SpyCloud 2026 Identity Exposure Report found that 65.7 billion identity records were recaptured in 2025 — a 23% year-over-year increase.
These numbers explain why identity-based attacks now dominate incident response engagements. Attackers do not need to exploit a vulnerability when they can log in with valid credentials. Every cloud application, SaaS platform, and federated identity provider expands the identity attack surface. And traditional security tools — firewalls, endpoint agents, network monitoring — were not built to detect an attacker who looks like a legitimate user.
How ITDR works
ITDR operates through a continuous cycle of data collection, behavioral analysis, threat detection, and automated response. Here is how the operational model breaks down.
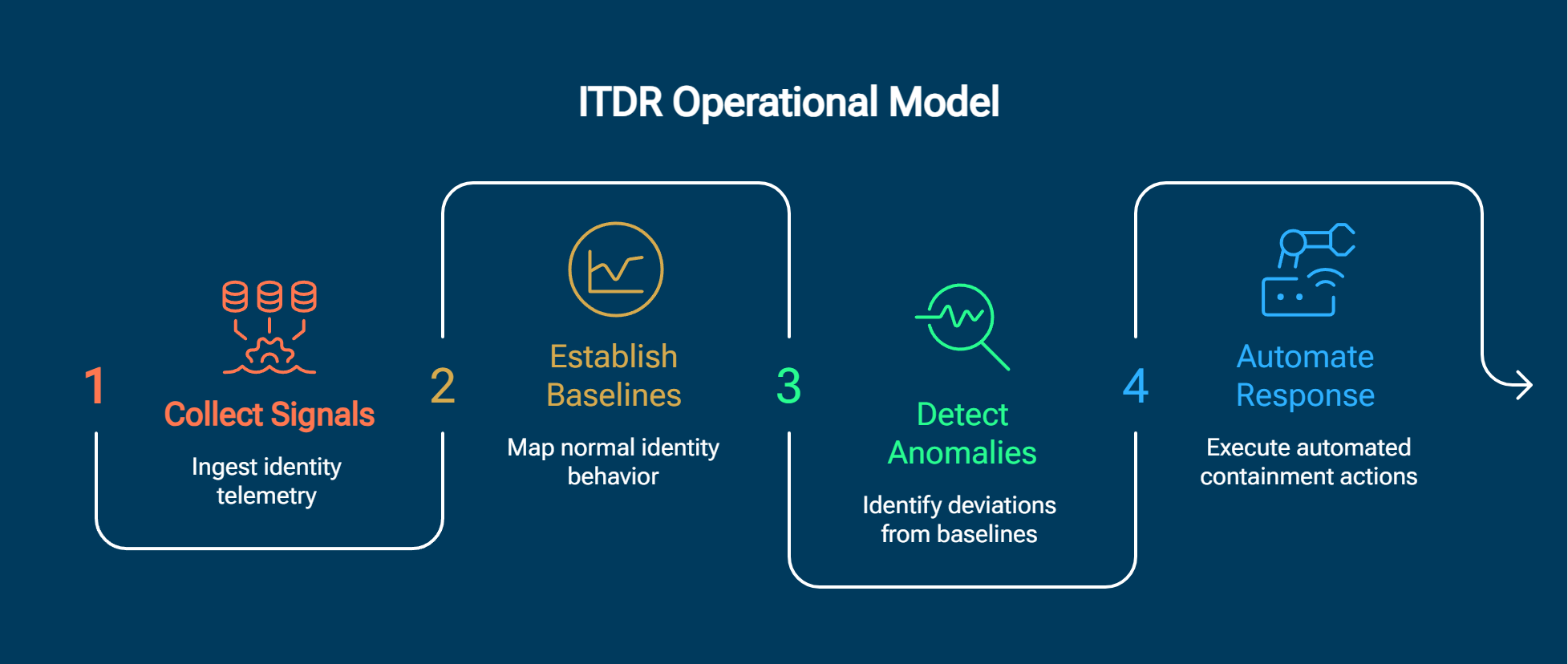
The four-phase ITDR operational model
- Collect identity signals. Ingest authentication logs and identity telemetry from Active Directory, cloud identity providers (such as Entra ID), SaaS applications, PAM tools, and federation services.
- Establish behavioral baselines. Map normal identity behavior patterns — login times, geographic locations, privilege usage, authentication methods, and access frequency — for each user and machine identity.
- Detect anomalies and threats. Apply behavioral threat detection to identify deviations such as impossible travel, unusual privilege escalation, abnormal OAuth consent grants, and password spraying patterns.
- Automate containment and response. Execute automated responses including step-up MFA challenges, account disablement, credential rotation, and session isolation based on threat severity.
- Correlate across identity sources. Stitch identity signals from on-premises and cloud environments to build unified threat detection context.
- Tune and optimize. Continuously refine detection thresholds, reduce false positives, and expand coverage as the identity attack surface evolves.
This cycle runs continuously. Unlike point-in-time audits, ITDR provides persistent monitoring that adapts as user behavior changes — new roles, new applications, new locations all trigger baseline recalibration.
Identity security posture management (ISPM)
ISPM is the preventive counterpart to ITDR's detective and responsive role. Where ITDR asks "is this identity behaving maliciously right now?", ISPM asks "are our identity configurations creating unnecessary risk?"
Key ISPM functions include identity inventory, permission right-sizing, misconfiguration detection, and dormant account identification. The need is acute. According to Unit 42's 2026 research, 99% of analyzed cloud identities had excessive permissions — a massive, exploitable attack surface that ISPM is designed to shrink before ITDR ever needs to detect an attacker leveraging those permissions.
Organizations that deploy both ITDR and ISPM together create a defense-in-depth model for identity. ISPM reduces the blast radius by eliminating unnecessary access. ITDR catches the threats that make it past preventive controls.
Types of identity-based attacks ITDR detects
Identity-based attacks span a wide range of techniques targeting both human and machine identities. ITDR is designed to detect these attacks through behavioral analytics rather than static rules.
Table: Identity-based attacks and ITDR detection methods
For deeper exploration of specific attack types, see the dedicated guides on credential theft, privilege escalation, lateral movement, account takeover, and Kerberoasting.
Non-human identity (NHI) threats
Non-human identities — API keys, service accounts, OAuth tokens, and AI agent credentials — now outnumber human identities by more than 10-to-1 in most enterprises. They represent a rapidly expanding blind spot.
The SpyCloud 2026 Identity Exposure Report revealed that 18.1 million exposed API keys and tokens were recaptured in 2025, alongside 6.2 million AI tool credentials exposed via infostealer malware. These machine credentials often have broad permissions, long or nonexistent expiration periods, and limited monitoring — making them high-value targets.
Key NHI attack vectors include OAuth token abuse, service account compromise, API key theft, and session cookie replay. ITDR solutions address NHI threats by baselining machine identity behavior and flagging deviations — an API key suddenly used from an unfamiliar IP range, a service account accessing resources outside its normal scope, or an AI agent credential being used at unusual hours.
ITDR vs. other security tools
Security teams already operate IAM, PAM, EDR, XDR, and SIEM platforms. ITDR does not replace any of them. It fills a specific gap — identity-specific behavioral detection — that none of these tools was designed to address.
Table: How ITDR relates to existing security tools
The key distinction is behavioral depth. IAM and PAM enforce policies. EDR watches endpoints. SIEM correlates logs. None of them apply continuous behavioral analytics specifically to identity signals across the full identity attack surface — on-premises Active Directory, cloud identity providers, SaaS applications, and federation services simultaneously.
Identity attacks in practice
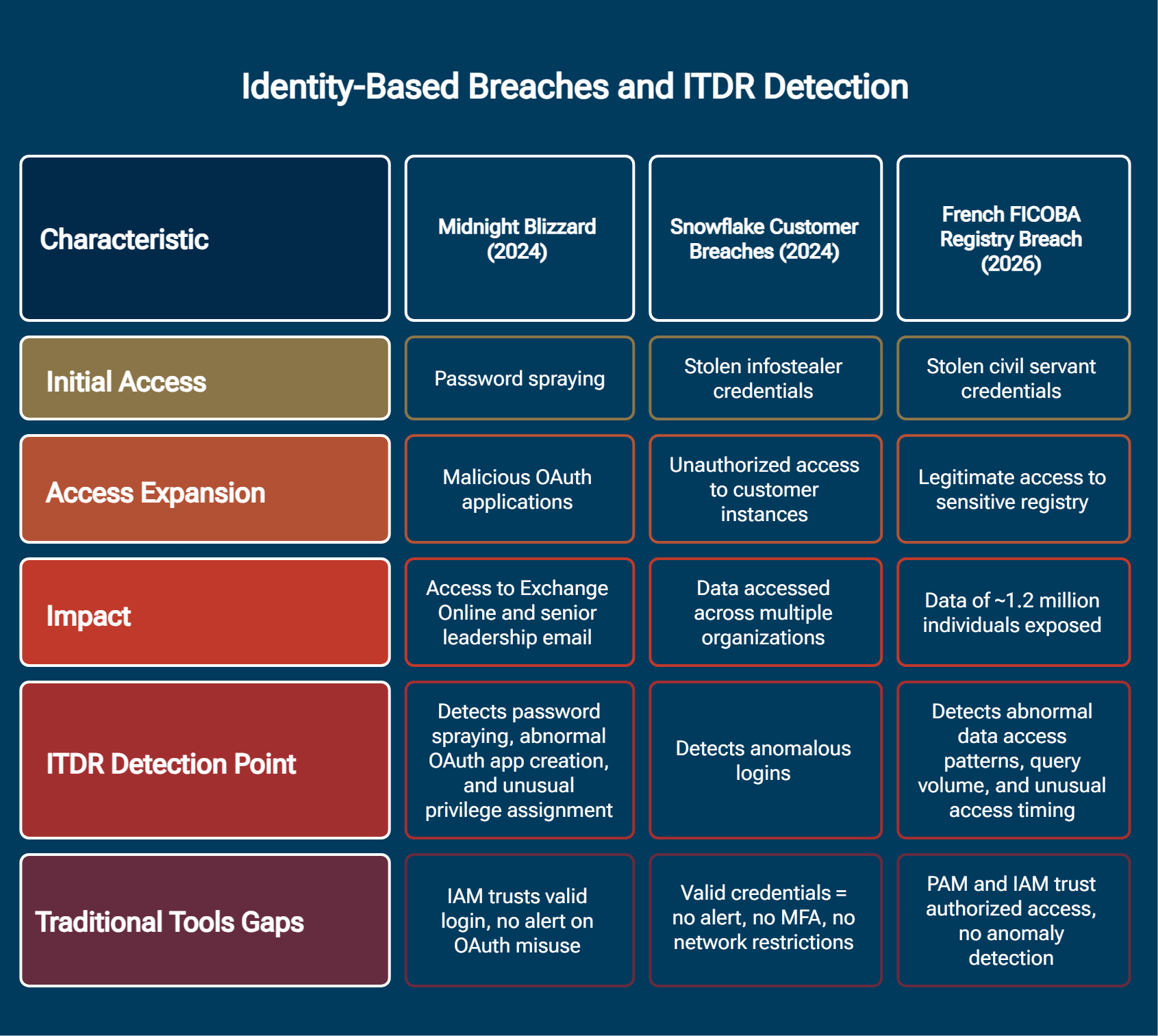
Real-world breaches demonstrate why ITDR matters more effectively than any theoretical discussion. Each of the following cases involved identity-based attacks that bypassed traditional controls — and each reveals specific points where ITDR would have detected the threat.
Snowflake customer breaches (2024)
Threat actor UNC5537 used infostealer-harvested credentials — some dating back to 2020 — to access approximately 165 customer instances on the cloud data platform. Affected organizations included major telecommunications, entertainment, and financial services companies.
Three factors enabled the breach. Customer accounts lacked MFA. Valid credentials from years-old infostealers still worked. No network access policies restricted login sources.
ITDR lesson. Behavioral analytics would have detected anomalous login patterns — new geolocations, unfamiliar devices, and known-compromised credentials — flagging the access attempts before data breach exfiltration began. Source: Cloud Security Alliance.
Midnight Blizzard (2024)
APT29 used password spraying to compromise a legacy test account that lacked MFA. From there, the threat actor leveraged legacy OAuth applications with elevated permissions to create malicious OAuth apps and grant them Exchange Online full access — ultimately reading senior leadership email.
ITDR lesson. ITDR would have detected the password spraying pattern, flagged the OAuth application creation from an unusual source, and alerted on the abnormal role assignment granting Exchange Online access. Multiple detection opportunities existed across the kill chain. Source: MSTIC incident guidance.
French FICOBA registry breach (2026)
An attacker used stolen civil servant credentials to access the national bank account registry (FICOBA), exposing financial data for approximately 1.2 million individuals. PAM alone could not detect the abuse because the attacker used valid credentials with authorized access levels.
ITDR lesson. Behavioral analytics would have flagged anomalous access patterns — unusual data volume, atypical query timing, and access frequency far exceeding the user's historical baseline. Source: The Hacker News.
Detecting and preventing identity threats
Effective identity threat detection requires phased implementation, measurable KPIs, and a deliberate choice between self-managed and managed approaches. Here are the best practices and a practical roadmap.
ITDR best practices:
- Continuously monitor all identity sources (Active Directory, cloud IdPs, SaaS, PAM)
- Integrate ITDR with existing SIEM and XDR platforms for correlated context
- Implement least privilege and enforce just-in-time access
- Deploy deception-based detection using honeypot accounts and honeytokens
- Develop identity-specific incident response playbooks
- Enable proactive threat hunting focused on identity signals
ITDR implementation roadmap
Table: Phased ITDR implementation roadmap
ITDR metrics and KPIs to track throughout implementation:
- MTTI (mean time to identify identity incidents): Target <1 hour for critical identity alerts
- MTTC (mean time to contain identity-based intrusions): Target <4 hours
- Identity attack surface coverage: Target >95% of identity sources monitored
- False positive rate: Target <10% of total identity alerts
- Detection-to-containment gap: An industry annual threat report found that 68% of organizations detect identity threats within 24 hours, but only 55% contain them effectively — a 13-point gap that ITDR automation is designed to close.
Managed ITDR for resource-constrained teams
Not every organization has the staffing to build and operate ITDR in-house. Managed detection and response services provide outsourced identity threat detection and response for teams that need 24/7 coverage without expanding headcount.
When to consider managed ITDR:
- Security teams with fewer than five FTEs
- Limited 24/7 monitoring coverage
- Insufficient identity security expertise in-house
What to evaluate: Coverage breadth (AD + cloud + SaaS), response SLAs, integration with the existing stack, and transparent reporting. The market for managed ITDR is growing rapidly, with multiple vendors expanding their managed ITDR capabilities to meet demand from MSPs and MSSPs.
ITDR and compliance
ITDR capabilities map directly to identity-related controls across major regulatory compliance frameworks. Aligning ITDR to these frameworks simplifies audit evidence collection and demonstrates proactive identity security governance.
MITRE ATT&CK identity technique mapping
Table: MITRE ATT&CK techniques covered by ITDR
For a broader overview of the framework, see the MITRE ATT&CK topic page.
Compliance framework crosswalk
Table: How ITDR maps to compliance frameworks
Future trends and emerging considerations
The identity threat landscape is evolving faster than most security programs can adapt. Over the next 12–24 months, several developments will reshape how organizations approach ITDR.
AI-accelerated attacks are compressing response windows. Unit 42's 2026 research found that AI-assisted attack simulations achieved full exfiltration in just 25 minutes, with the fastest observed real-world exfiltration at 72 minutes. These timelines leave no room for manual investigation. ITDR solutions that automate detection and response will become table stakes, not differentiators.
PAM and ITDR convergence is accelerating. Both Gartner and KuppingerCole now recommend unified identity defense layers that merge privileged access controls with identity threat detection. Organizations that keep these capabilities siloed will face gaps that attackers already know how to exploit.
Session-based attacks are scaling through phishing-as-a-service. The Tycoon 2FA platform — which Europol disrupted in a coordinated takedown — enabled adversary-in-the-middle attacks that bypassed MFA at scale. Despite the disruption, the platform returned within weeks, demonstrating the resilience of the phishing-as-a-service economy. ITDR must detect session hijacking and token replay regardless of how the initial credential was compromised.
Non-human identity protection will become a regulatory requirement. As API keys, service accounts, and AI agent credentials proliferate, expect compliance frameworks to mandate monitoring and lifecycle management for machine identities. Organizations should begin inventorying their NHI attack surface now.
Modern approaches to identity threat detection
The most effective ITDR programs today go beyond standalone identity monitoring. They integrate identity signals with network detection and response, cloud telemetry, and endpoint context to build a unified view of attacker behavior across the entire attack surface.
Cloud-native ITDR extends detection to cloud identity providers, SaaS platforms, and multi-cloud environments where traditional on-premises tools have no visibility. AI security capabilities — including AI-driven threat intelligence and behavioral modeling — enable ITDR solutions to keep pace with adversaries who are themselves using AI to accelerate attacks.
The integration of ITDR with zero trust architectures represents a natural evolution. Zero trust mandates continuous verification. ITDR provides the identity behavioral intelligence that makes continuous verification meaningful rather than performative.
How Vectra AI approaches identity threat detection
Vectra AI's approach to identity threat detection centers on Attack Signal Intelligence, which applies behavioral analytics to identity signals across on-premises Active Directory, cloud identity providers, and SaaS applications. By correlating identity behaviors with network telemetry, the methodology identifies real attacks hiding in normal-looking identity activity rather than generating more alerts for analysts to triage. The goal is signal over noise — giving security teams the clarity to act on what matters and the confidence to ignore what does not.
Conclusion
Identity-based attacks are not a trend. They are the dominant attack vector — responsible for the majority of initial access in confirmed incidents and the root cause of high-profile breaches at organizations of every size and industry. The Snowflake, Midnight Blizzard, and FICOBA cases each tell the same story — valid credentials, insufficient monitoring, and preventive controls that were never designed to catch an attacker who looks like a legitimate user.
ITDR closes that gap. It brings continuous behavioral detection to the identity attack surface, catches threats that IAM, PAM, and EDR cannot see, and automates containment before attackers achieve their objectives. Combined with ISPM for preventive posture management and aligned to frameworks like MITRE ATT&CK and NIST CSF, ITDR gives security teams the visibility and speed they need to defend the most targeted surface in modern enterprises.
For organizations ready to evaluate their identity threat detection capabilities, explore how Vectra AI approaches ITDR through Attack Signal Intelligence.
FAQs
What is identity threat detection and response (ITDR)?
Identity threat detection and response (ITDR) is a security discipline that detects, analyzes, and responds to threats targeting user and machine identities. It uses behavioral analytics and AI to identify credential misuse, privilege escalation, and identity-based lateral movement across on-premises and cloud environments.
Unlike identity and access management (IAM), which controls who gets access, ITDR focuses on detecting when that access is being abused. It monitors authentication events, authorization patterns, and identity behaviors across Active Directory, cloud identity providers, and SaaS applications to identify threats that traditional perimeter and endpoint tools miss.
Gartner first recognized ITDR as a distinct security category in 2022, and the market has since grown at over 22% CAGR. The discipline has become essential as identity-based attacks now account for the majority of initial access in confirmed incidents.
How does ITDR differ from EDR?
Endpoint detection and response (EDR) monitors endpoints — workstations, servers, and mobile devices — for malicious processes, file system changes, and anomalous behaviors at the device level. ITDR monitors identity signals across the full identity infrastructure — Active Directory, cloud IdPs, SaaS applications, and federation services — to detect credential abuse and identity-based attacks.
The critical difference lies in what each tool can see. When an attacker uses valid credentials stolen via an infostealer to log in from a new device, EDR sees a normal authentication event on the endpoint. ITDR sees an anomalous login — new geolocation, unfamiliar device fingerprint, credentials flagged in known breach databases — and raises an alert. Many modern attacks are designed to avoid triggering endpoint detections entirely, which is precisely why ITDR exists as a complementary layer.
Why is ITDR important?
Identity-based attacks now dominate the threat landscape. In 2025, 90% of incident response engagements involved identity weaknesses, and 65% of initial access was identity-driven, according to Unit 42's Global Incident Response Report 2026. Traditional tools like IAM enforce access policies but cannot detect when those policies are circumvented. EDR monitors endpoints but has limited visibility into cloud identity activity, OAuth consent grants, and federated authentication flows.
ITDR fills this gap by applying continuous behavioral analytics to identity signals. It detects threats that bypass preventive controls — stolen credentials that pass MFA, compromised service accounts, OAuth token abuse, and privilege escalation through legitimate-looking administrative actions. Without ITDR, organizations rely on post-incident forensics rather than real-time detection.
What is identity security posture management (ISPM)?
ISPM is the preventive counterpart to ITDR. While ITDR detects and responds to active identity threats in real time, ISPM proactively identifies and remediates identity misconfigurations, excessive permissions, and dormant accounts before attackers can exploit them.
Key ISPM capabilities include identity inventory management, permission right-sizing, misconfiguration detection, and dormant account identification. The 2026 Unit 42 research found that 99% of analyzed cloud identities had excessive permissions — an enormous attack surface that ISPM is designed to reduce. When combined with ITDR, organizations establish a defense-in-depth model where ISPM shrinks the exploitable surface and ITDR catches threats that make it past preventive controls.
What is managed ITDR?
Managed ITDR is an outsourced security service where a provider operates identity threat detection and response on behalf of an organization. It is designed for teams with fewer than five security FTEs who need 24/7 identity threat monitoring without building in-house capability.
Managed ITDR providers typically cover Active Directory, cloud identity providers, and SaaS applications. When evaluating managed ITDR services, organizations should assess coverage breadth, response SLAs, integration with their existing security stack, and the transparency of reporting and investigation workflows. The market for managed ITDR is growing rapidly as MSPs and MSSPs expand their identity security offerings to meet demand from resource-constrained organizations.
What are the key ITDR metrics?
Key ITDR metrics include mean time to identify identity incidents (MTTI), mean time to contain identity-based intrusions (MTTC), false positive rate for identity alerts, percentage of identity attack surface covered, and the detection-to-containment gap. Industry research indicates that 68% of organizations detect identity threats within 24 hours, but only 55% contain them effectively — a 13-point gap that ITDR automation is designed to close.
Recommended targets include MTTI under one hour for critical identity alerts, MTTC under four hours, false positive rates below 10%, and identity attack surface coverage above 95%. These KPIs should be tracked from the assessment phase onward and reported regularly to security leadership.
How does ITDR map to MITRE ATT&CK?
ITDR covers MITRE ATT&CK techniques across multiple tactics relevant to identity-based attacks. In Initial Access, ITDR detects T1078 (Valid Accounts) by identifying anomalous logon patterns. In Credential Access, it detects T1110 (Brute Force) and T1558 (Steal or Forge Kerberos Tickets). In Lateral Movement, it detects T1550 (Use Alternate Authentication Material) including pass-the-hash and token replay. In Persistence, it detects T1098 (Account Manipulation) through monitoring unauthorized role changes and permission modifications.
This mapping provides defenders with a framework for assessing ITDR coverage gaps and aligning detection capabilities to the specific techniques adversaries use against identity infrastructure.