Zero-day vulnerabilities explained: what they are, how they work, and how to defend against them
Key insights
- 90 zero-day vulnerabilities were exploited in the wild in 2025, with 48% targeting enterprise technologies — an all-time high driven by attacks on edge devices and security appliances (GTIG 2025).
- The exploit-to-patch gap is critical. Attackers weaponize vulnerabilities in five days on average, but organizations take 60 to 150 days to deploy patches.
- Commercial surveillance vendors now surpass state-sponsored groups as the leading source of attributed zero-day exploitation, responsible for 18 of 42 attributed exploits in 2025.
- Signature-based detection cannot stop zero-day attacks. Behavioral analytics, network detection, and zero trust architecture form the foundation of effective defense.
- AI is reshaping both sides of the equation, accelerating exploit discovery for attackers while enabling behavioral detection that does not rely on known indicators.
In 2025, Google's Threat Intelligence Group tracked 90 zero-day vulnerabilities exploited in the wild — with enterprise technologies reaching an all-time high of 48% of all targets. Edge devices, security appliances, and networking infrastructure bore the brunt of attacks that signature-based defenses simply could not see coming.
For security teams, zero-day vulnerabilities represent the ultimate blind spot. You cannot write a detection signature for something nobody knows exists. And with the average time to weaponize a disclosed vulnerability collapsing to five days — while organizations still take 60 to 150 days to patch — the gap between attacker speed and defender response has never been wider.
This guide breaks down how zero-day exploits work, who is buying and selling them, what recent attacks reveal about the shifting threat landscape, and how to build defenses that do not depend on knowing the threat in advance.
What is a zero-day vulnerability?
A zero-day vulnerability is a software security flaw that is unknown to the vendor and for which no patch exists, giving defenders zero days of warning before attackers can exploit it. The term "zero-day" refers to the fact that the software maker has had zero days to fix the problem when exploitation begins. The National Institute of Standards and Technology (NIST) formally defines a zero-day attack as one that exploits a previously unknown vulnerability.
Understanding zero-day threats requires distinguishing three related but distinct concepts. The zero-day vulnerability is the flaw itself — an unknown bug in software, hardware, or firmware. The zero-day exploit is the technique or code an attacker uses to take advantage of that flaw. And the zero-day attack is the real-world incident that results from deploying the exploit against a target.
This distinction matters because a vulnerability can exist for years before anyone discovers it. It only becomes a zero-day threat when an attacker (or researcher) identifies and weaponizes it.
Key terminology
- Zero-day vulnerability: The unknown flaw in software, hardware, or firmware that creates a security gap.
- Zero-day exploit: The attack code or technique that leverages the unknown flaw to gain unauthorized access or execute commands. Learn more about exploits and how they are used in attack chains.
- Zero-day attack: The incident in which an attacker deploys the exploit against a target system or organization.
- Zero-day malware: Malware that leverages a previously unknown vulnerability to deliver malicious payloads, evading conventional antivirus because no signature exists for the exploit or payload.
The scale of the problem is significant. Google's Threat Intelligence Group tracked 90 zero-day vulnerabilities exploited in the wild in 2025, with 48% targeting enterprise technologies. For the fifth consecutive year, exploits were the number one initial access vector, responsible for 33% of all intrusions investigated by Mandiant.
How zero-day exploits work
A zero-day exploit follows a lifecycle that creates multiple windows of risk for organizations. Understanding each stage helps security teams identify where defenses can be applied.
The zero-day vulnerability lifecycle progresses through six stages:
- Introduction — A coding error or design flaw is introduced during software development.
- Discovery — The vulnerability is found by security researchers, threat actors, or automated tools.
- Exploitation — If attackers find it first, they develop and deploy an exploit before anyone else knows the flaw exists.
- Disclosure — The vulnerability is reported to the vendor (responsible disclosure) or made public.
- Patch release — The vendor develops and publishes a security update.
- Patch adoption — Organizations test and deploy the patch across their environments.
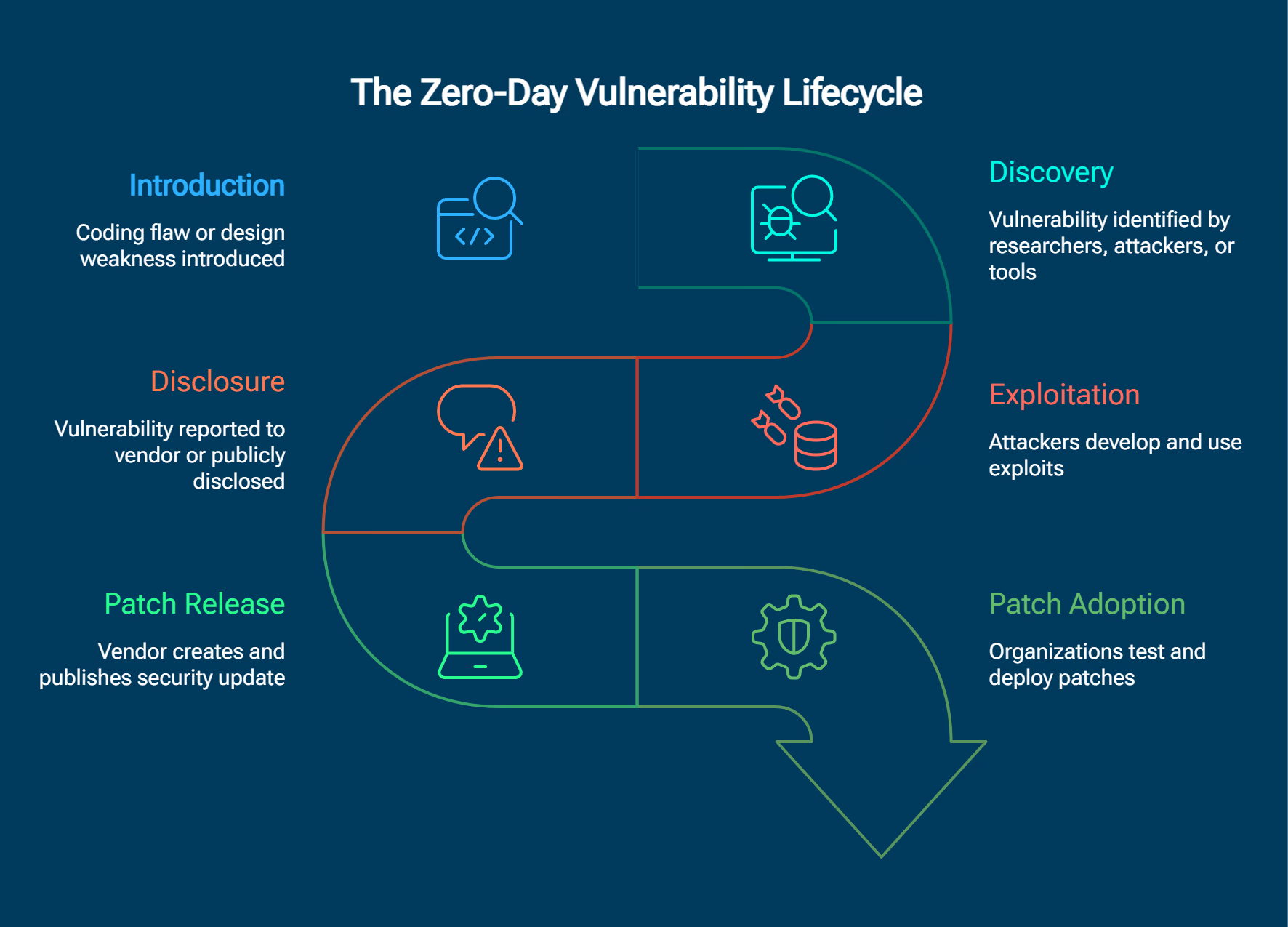
The window of vulnerability — the period between when a flaw is introduced and when a patch is widely deployed — averages 312 days. During this time, attackers can operate freely against unprotected systems.
What makes the current landscape particularly dangerous is the collapse in time-to-exploit. The average time to weaponize a disclosed vulnerability dropped to five days in 2023, down from 63 days in 2018–2019. Meanwhile, organizations still take an average of 60 to 150 days to deploy patches. This mismatch creates a dangerous gap where attackers move at machine speed while defenders move at committee speed.
Proper vulnerability management processes can reduce this gap, but they cannot eliminate it for true zero-day scenarios where no patch exists.
The disclosure dilemma
How and when vulnerabilities are disclosed is one of cybersecurity's most consequential debates. Google Project Zero uses a 90-day standard disclosure window, with a 30-day grace period for complex patches. However, for vulnerabilities under active exploitation, they apply a more aggressive seven-day policy — recognizing that when attackers are already using a flaw, waiting 90 days puts defenders at unacceptable risk.
The Trend Zero Day Initiative (ZDI) and CERT/CC maintain their own disclosure timelines. The industry has largely settled on a tiered approach: seven days for active exploitation, and 90 days with extensions for standard disclosure. Even so, the debate continues about whether 90 days is too generous when exploit timelines keep shrinking.
Zero-day vs. n-day vulnerabilities
While zero-day vulnerabilities dominate headlines, n-day vulnerabilities — known flaws with available patches that remain undeployed — cause far more widespread damage in practice. Understanding this distinction changes how organizations should prioritize their defenses.
Table: Key differences between zero-day, n-day, and one-day vulnerabilities.
The real-world implication is clear. The five-day average time-to-exploit vastly outpaces the 60 to 150-day average patching cycle. Every disclosed vulnerability immediately enters a race between defenders deploying patches and attackers weaponizing the flaw. For the majority of organizations, the attackers win that race.
This means that even after a zero-day is disclosed and patched, it transitions into an n-day vulnerability that remains exploitable across most environments for weeks or months. Defense strategies must account for both the zero-day phase (no signature, no patch) and the n-day phase (patch exists but is not deployed).
Types of zero-day targets
The targets of zero-day exploitation have shifted dramatically. According to GTIG's 2025 analysis, enterprise technologies reached an all-time high of 48% of all zero-day targets — a trend with significant implications for network security strategy.
Of the 90 zero-days tracked in 2025, 47 targeted end-user platforms (browsers, mobile operating systems, desktop operating systems) while 43 targeted enterprise technologies. Within the enterprise category, security and networking products accounted for 21 of the 43 enterprise-targeted zero-days, and at least 14 targeted edge devices including routers, switches, and security appliances.
Table: Most-targeted vendors by zero-day exploitation in 2025 (GTIG).
This shift matters for defenders because edge devices and security appliances typically lack endpoint detection and response (EDR) coverage. Traditional endpoint security tools cannot monitor the firmware or embedded operating systems running on routers, firewalls, and SD-WAN controllers. When these devices are compromised through zero-day exploits, the attack can go undetected unless organizations have network-level visibility into the behavioral patterns that follow exploitation.
Zero-day exploit market economics
A thriving market ecosystem surrounds zero-day exploits, with prices reflecting the extraordinary value attackers place on unknown vulnerabilities. Understanding this market helps organizations assess the caliber of threats they face.
Buyer categories span four segments:
- Governments and intelligence agencies purchase zero-days for offensive cyber operations and surveillance
- Commercial surveillance vendors (CSVs) develop and sell spyware incorporating zero-day exploits to government clients
- Criminal organizations buy exploits on dark web marketplaces for financial gain
- Bug bounty programs offer legal alternatives, though payouts are typically a fraction of exploit broker prices
Table: Reported zero-day exploit pricing by target type (2024–2026).
Prices are rising as vendors harden their products, making new zero-days harder to discover and more valuable when found.
A landmark shift occurred in 2025: commercial surveillance vendors surpassed state-sponsored groups in attributed zero-day exploitation for the first time. CSVs were attributed to 18 of 42 attributed exploits, compared to 12 for state-sponsored groups. This means the commercial spyware market — companies selling surveillance tools to government clients worldwide — now drives more zero-day exploitation than traditional nation-state hacking operations.
Zero-day vulnerabilities in practice
Recent zero-day exploitation patterns reveal a clear trend: attackers increasingly target the infrastructure components that defenders rely on. These 2025–2026 examples illustrate distinct attack patterns that organizations should study.
Cisco Catalyst SD-WAN (CVE-2026-20127) — A critical authentication bypass vulnerability in Cisco's SD-WAN platform was exploited by threat actor UAT-8616 since at least 2023. The attackers compromised controllers and added malicious rogue peers to targeted networks. Because SD-WAN controllers lack traditional EDR coverage, this exploitation persisted for years before discovery.
Dell RecoverPoint (CVE-2026-22769) — Mandiant discovered this zero-day while investigating compromised Dell RecoverPoint systems communicating with command and control servers associated with BRICKSTORM and GRIMBOLT backdoors. Linked to China-aligned threat actors, the exploitation had been ongoing since mid-2024 — demonstrating how zero-day attacks can persist undetected for over a year without proper network monitoring.
Microsoft February 2026 Patch Tuesday — Microsoft addressed roughly 60 vulnerabilities in one patch cycle, including six actively exploited zero-days. The volume of simultaneous zero-days from a single vendor underscores the need for robust triage processes when multiple critical patches emerge at once.
FortiCloud SSO bypass (CVE-2026-24858) — A critical authentication bypass in a major security vendor's cloud SSO product was actively exploited before disclosure. This case is particularly instructive because it targeted the security infrastructure itself — undermining a tool that organizations relied on for defense.
Table: Major zero-day disclosures and patches in Q1 2026.
The lesson across these cases is consistent: edge devices and security appliances lack endpoint protection, and organizations need incident response plans that account for compromise of their own security tools. GTIG data shows zero-day exploitation volume has stabilized at elevated levels — 100 in 2023, 78 in 2024, 90 in 2025 — meaning enterprises face multiple new zero-day threats every month.
AI's dual role in zero-day discovery and defense
AI is fundamentally transforming both sides of the zero-day equation. On offense, AI accelerates vulnerability discovery and exploit development. On defense, AI enables detection approaches that do not depend on knowing the threat in advance. Google's Threat Intelligence Group assessed that AI will "accelerate the ongoing race between attackers and defenders" through 2026 and beyond.
Offensive: AI-accelerated exploitation
AI-assisted fuzzing and code analysis can discover vulnerabilities at a scale and speed that human researchers cannot match. Large language models trained on codebases can identify memory corruption bugs, logic flaws, and authentication bypasses that would take human analysts weeks to find. This means the supply of discoverable zero-days is increasing even as vendors improve their security practices.
The implications are serious. As AI tools become more capable, the barrier to discovering exploitable vulnerabilities drops. Threat actors who previously lacked the technical sophistication to find zero-days can now augment their capabilities with AI-powered discovery.
Defensive: behavioral detection without signatures
The fundamental challenge of zero-day defense is what some researchers call the cybersecurity catch-22: you cannot write a signature for something you do not know exists. This is exactly where AI threat detection and behavioral analytics become essential.
AI-powered threat detection identifies the behavioral patterns that follow exploitation — lateral movement, privilege escalation, command and control communication, data staging, and exfiltration — regardless of the specific vulnerability or exploit used. By focusing on what attackers do after gaining access rather than how they get in, behavioral detection provides coverage against zero-day exploitation without requiring prior knowledge of the specific flaw.
This approach is particularly critical for enterprise technologies like edge devices and security appliances, which accounted for the majority of enterprise zero-day targets in 2025 and typically lack endpoint-level protection.
Detecting and defending against zero-day attacks
Because zero-day vulnerabilities are unknown by definition, defending against them requires strategies that do not depend on prior knowledge of the specific threat. Traditional antivirus and signature-based tools cannot detect zero-day attacks — they require known indicators to function, and zero-days provide none.
Effective zero-day defense combines multiple layers:
- Deploy behavioral threat detection to identify anomalous activity patterns
- Implement network detection and response for visibility into unmanaged devices
- Adopt zero trust architecture to limit lateral movement after initial access
- Prioritize rapid patching using the CISA Known Exploited Vulnerabilities catalog
- Monitor edge devices and security appliances with network-level analytics
- Conduct proactive threat hunting focused on behavioral indicators
- Segment networks to contain the blast radius of any single compromise
Table: Comparison of zero-day detection approaches.
Why signature-based detection fails
Signature-based detection matches known malicious patterns — file hashes, network signatures, or behavioral rules — against incoming activity. By definition, zero-day exploits have no known signature. This means conventional antivirus, basic intrusion detection systems, and static rule-based SIEM detections are ineffective against zero-day attacks.
Behavioral analytics and anomaly detection take a fundamentally different approach. Instead of asking "have we seen this threat before?" they ask "does this activity match normal patterns?" When a compromised edge device begins communicating with an unfamiliar external server at unusual hours, or when a service account suddenly accesses resources it has never touched before, behavioral detection flags the anomaly — regardless of whether anyone has ever seen the specific exploit.
CISA added over 190 new entries to the Known Exploited Vulnerabilities catalog in 2025, underscoring the volume of newly discovered exploits requiring rapid organizational response.
Zero-day vulnerabilities and compliance
Organizations must map their zero-day response capabilities to the regulatory frameworks governing their industry. Failure to demonstrate adequate controls for vulnerability response can carry significant consequences.
Table: Zero-day response mapped to cybersecurity frameworks.
Meeting compliance requirements demands more than patching alone. Organizations need to demonstrate that they maintain detection capabilities for unknown threats, not just known vulnerabilities. Security frameworks like NIST CSF explicitly call for baseline network behavior monitoring (DE.AE-1) — a control directly relevant to zero-day detection.
Modern approaches to zero-day defense
The industry is shifting from signature-based prevention to behavioral, AI-driven detection as the foundation of zero-day defense. This shift reflects a recognition that when 48% of zero-days target enterprise technologies — many of which lack endpoint protection — network-level visibility becomes the primary detection layer.
Organizations building modern zero-day defenses focus on three principles. First, assume compromise and design detection around attacker behaviors that follow exploitation, not the exploitation itself. Second, ensure visibility across the entire attack surface, including edge devices, cloud infrastructure, and identity systems that traditional endpoint tools cannot cover. Third, invest in network detection and response capabilities that analyze traffic patterns and behavioral anomalies in real time.
Looking ahead, the EU Cyber Resilience Act (effective 2027) will impose new vulnerability disclosure requirements on software vendors, potentially accelerating the timeline from discovery to public awareness — and further compressing the window defenders have to respond.
How Vectra AI approaches zero-day defense
Vectra AI's Attack Signal Intelligence monitors network, identity, and cloud behavior patterns to detect zero-day exploitation in progress. Rather than relying on signatures for known threats, this approach identifies the attacker behaviors that follow exploitation — lateral movement, privilege escalation, command and control communications, and data exfiltration — regardless of the initial access method. This assume-compromise philosophy aligns with the reality that edge devices and security appliances — the primary enterprise zero-day targets in 2025 — typically lack EDR coverage, making behavioral network analysis the most effective detection layer.
Conclusion
Zero-day vulnerabilities remain the most consequential blind spot in enterprise security. With 90 exploited in the wild in 2025, commercial surveillance vendors surpassing nation-state groups in attribution, and enterprise technologies absorbing nearly half of all zero-day attacks, the threat landscape demands a fundamental shift in defensive strategy.
The data is clear: signature-based approaches alone cannot protect organizations against threats that have never been seen before. The five-day exploit window, the 60 to 150-day patching gap, and the increasing focus on edge devices without endpoint protection all point to the same conclusion. Effective zero-day defense requires behavioral detection across the full attack surface, zero trust architecture to limit blast radius, and the assumption that compromise is not a matter of if, but when.
Organizations that build their security posture around finding attacker behaviors — lateral movement, privilege escalation, command and control, and exfiltration — rather than matching known signatures position themselves to detect zero-day exploitation regardless of the specific vulnerability or exploit involved.
Explore how Vectra AI detects threats that bypass traditional security controls.
Related cybersecurity fundamentals
FAQs
How long does a zero-day last?
The "window of vulnerability" — the period from when a flaw is introduced until a patch is widely deployed — averages 312 days according to lifecycle research. However, the timeline varies significantly depending on the stage. Once a zero-day is publicly disclosed, vendors typically release a patch within seven to 14 days for actively exploited vulnerabilities. The real bottleneck is patch adoption: organizations take an average of 60 to 150 days to deploy security updates across their environments. This means that even after a zero-day transitions to a known vulnerability with an available patch, most organizations remain exposed for weeks or months. During the pre-disclosure phase, zero-day exploitation can persist for years if no one detects the malicious activity — as demonstrated by the Dell RecoverPoint case where exploitation continued undetected from mid-2024 to early 2026.
Are zero-day attacks common?
Google's Threat Intelligence Group tracked 90 zero-day vulnerabilities exploited in the wild in 2025, consistent with a four-year range of 60 to 100 annually (100 in 2023, 78 in 2024). While any single zero-day is a rare and high-value asset, the cumulative volume means enterprises face multiple new zero-day threats each month. The apparent stabilization around 60 to 100 annual zero-days likely represents a floor rather than a ceiling, as many zero-day exploits are never discovered or publicly attributed. Tracking organizations like GTIG, Mandiant, and ZDI may report different counts based on their methodology and visibility.
What is a zero-day patch?
A zero-day patch is an emergency security update released to fix a vulnerability that was already being exploited before the vendor knew about it. Because the vulnerability is under active attack, vendors typically release these patches as out-of-band (unscheduled) updates rather than waiting for their regular patch cycle. Microsoft's February 2026 Patch Tuesday, for example, addressed six actively exploited zero-days in a single release. Organizations should prioritize zero-day patches above all other security updates and aim to deploy them within 24 to 48 hours rather than following standard change management timelines. CISA's BOD 22-01 establishes specific remediation timelines for federal agencies when zero-day patches are released for Known Exploited Vulnerabilities.
What is zero-day malware?
Zero-day malware is malicious software that exploits a previously unknown vulnerability to deliver its payload. Unlike traditional malware that can be detected by antivirus signatures, zero-day malware evades conventional detection because no signature exists for the exploit it leverages. This makes it particularly dangerous for organizations that rely primarily on signature-based security tools. Zero-day malware often appears in targeted attacks against high-value organizations rather than mass campaigns, because the zero-day exploits that enable it are expensive and limited in supply. Effective defense against zero-day malware requires behavioral detection approaches that identify suspicious activity patterns — such as unusual process execution, unexpected network connections, or anomalous file access — rather than matching known malicious signatures.
What is the zero-day vulnerability lifecycle?
The lifecycle progresses through six stages. First, a vulnerability is introduced during software development through a coding error or design flaw. Second, the vulnerability is discovered — either by security researchers conducting audits, threat actors hunting for exploitable flaws, or increasingly by AI-powered fuzzing tools. Third, if attackers discover the vulnerability before the vendor, they develop and deploy exploits. Fourth, the vulnerability is disclosed either through responsible disclosure to the vendor or public exposure. Fifth, the vendor develops and releases a security patch. Sixth, organizations test and deploy the patch across their environments. The highest-risk period spans from exploitation through patch adoption, where attackers are actively using the flaw while many organizations remain unpatched.
What is a zero-day exploit in simple terms?
A zero-day exploit is an attack that takes advantage of a software flaw the software maker does not know about yet. Because no fix exists, defenders have "zero days" to prepare before the attack can succeed. Think of it like a burglar finding an unlocked door that the homeowner did not know was there — the homeowner cannot lock a door they do not know exists. In cybersecurity terms, the software vendor cannot patch a bug they have not discovered, and security tools cannot block an attack they have never seen before. This is what makes zero-day exploits so valuable to attackers and so dangerous for organizations. Prices for zero-day exploits range from hundreds of thousands of dollars to over $9 million depending on the target, reflecting the significant advantage they give attackers.
Does cyber insurance cover zero-day attacks?
Coverage varies significantly by policy and incident circumstances. Many cyber insurance policies include exclusions for "acts of war" or "nation-state attacks," which overlap with a significant portion of zero-day scenarios — state-sponsored groups and commercial surveillance vendors account for the majority of attributed zero-day exploitation. Organizations should carefully review their policy language around these exclusions. Additionally, some policies may require that the insured organization demonstrate "reasonable security measures" were in place, which could include maintaining current patch levels, deploying behavioral detection tools, and following framework-aligned security practices. Organizations facing zero-day risk should work with their insurance brokers to understand exactly which scenarios are covered, what incident response requirements the policy mandates, and whether coverage extends to zero-day attacks attributed to nation-state actors.